April’s exploits were driven less by smart contract bugs and more by social engineering, bridge spoofing, and AI-assisted reconnaissance.
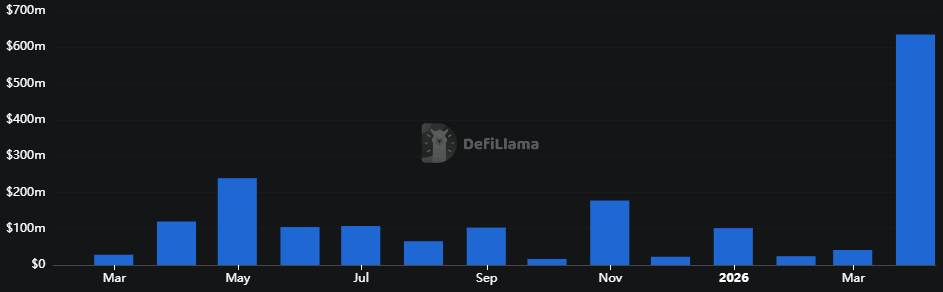
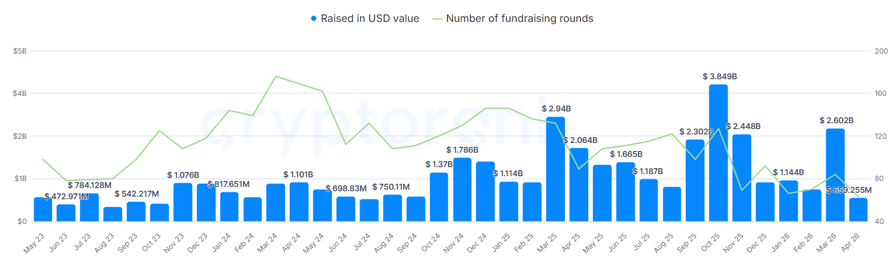
DeFi protocols and crypto infrastructure suffered 28 separate exploits totaling $635.2 million in April, the highest monthly incident count ever recorded by DefiLlama and roughly four times the $167 million stolen across the entire first quarter.
The incident count nearly doubled the previous monthly peak of 15, set just one month earlier.

In dollar terms, April ranks as the sixth-largest month on record, but the concentration was extreme: the $293 million Kelp DAO bridge exploit on April 18 and the $285 million Drift Protocol drain on April 1 accounted for $578 million, or 91% of the monthly total. TRM Labs has linked both attacks to North Korea, and now estimates that DPRK-affiliated actors are responsible for 76% of all crypto hack losses recorded in 2026, with cumulative theft exceeding $6 billion since 2017.
The Kelp incident, in which an attacker forged a cross-chain message through the protocol’s LayerZero bridge to release 116,500 rsETH against no source-chain backing, triggered the largest coordinated industry response of the cycle, with the DeFi United coalition raising over $300 million to restore rsETH’s backing.
Beyond the two headline events, the long tail of April incidents underscored a broadening attack surface. Rhea Lend lost $18.4 million on April 16 to a fake-collateral exploit, sanctioned Russia-linked exchange Grinex was drained of $15 million in a hot wallet breach the same day, and Wasabi Perps closed the month with a $5.5 million admin key compromise on April 30.
Is AI to Blame?
A growing number of analysts are pointing to AI as a structural driver behind the surge.
TRM noted in its report that North Korean operators appear to be incorporating AI tools into reconnaissance and social engineering workflows, consistent with the multi-month staging behind the Drift attack.
Independent analyst DefiIgnas argued that the broad sweep of smaller exploits also fits an AI-assisted pattern, with attackers likely using frontier models to scan for protocols that are rarely updated, share vulnerabilities with previously hacked projects, and hold at least $100,000 in their contracts. The Sweat Foundation contract on NEAR, drained for $3.5 million on April 29, fit that profile, with its core DeFi feature last updated seven months before the exploit.
The shift away from smart contract bugs toward operational and human attack vectors continued to define the month. Of the 28 incidents tracked, the largest losses stemmed from infrastructure-level compromises rather than code vulnerabilities, with social engineering of multisig signers, bridge message spoofing, and admin key compromises driving most of the damage.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.