The liquid restaking protocol argues that the 1-of-1 verifier setup at the center of the April 18 exploit was LayerZero’s own documented default.
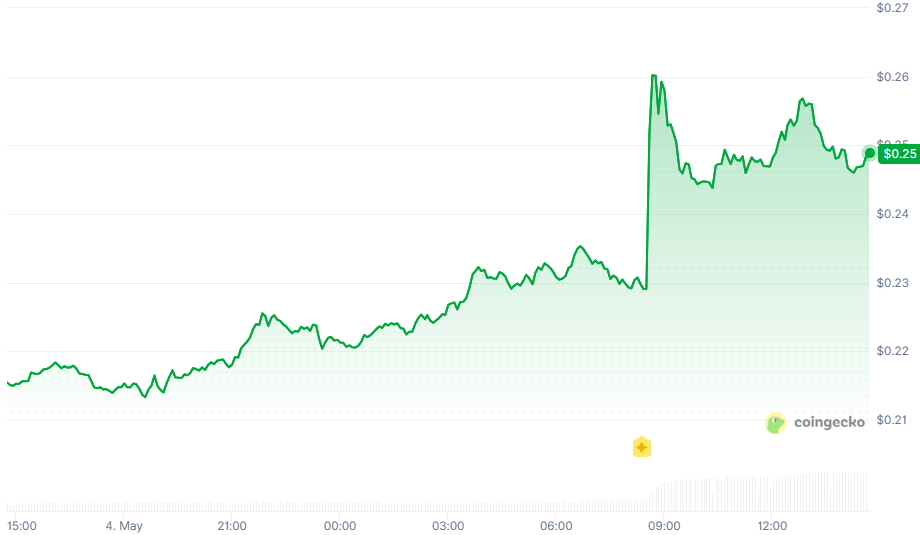
Kelp DAO on Tuesday published a detailed rebuttal to LayerZero’s account of the April 18 rsETH bridge exploit, confirming that it will migrate rsETH from the LayerZero OFT standard to Chainlink’s Cross-Chain Token (CCT) standard and accusing the cross-chain messaging firm of “blaming users for an issue that was caused by their own infrastructure failure.”
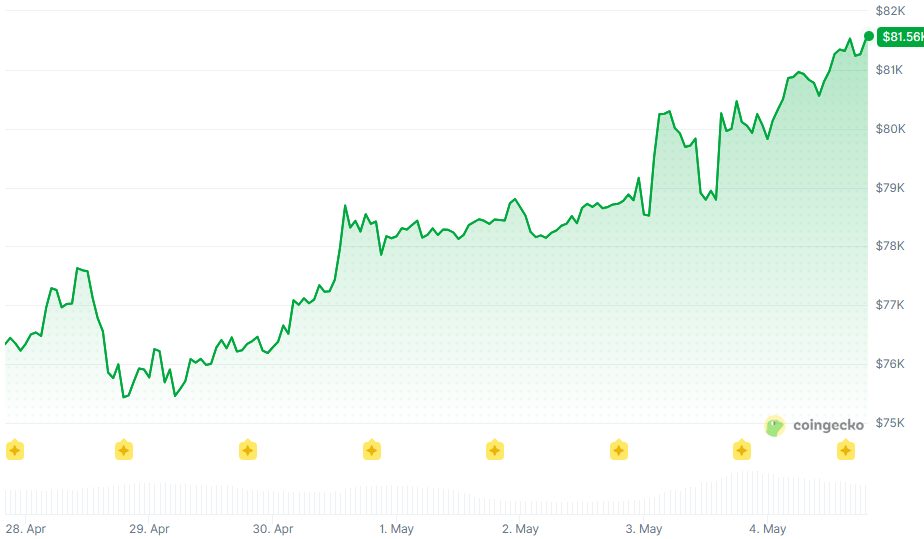
The statement, titled “Setting the Record Straight,” disputes nearly every claim in LayerZero’s post-mortem, which attributed the $300 million theft to Kelp’s choice of a 1-of-1 DVN configuration. Kelp argues that setup was the configuration LayerZero itself shipped as the default, approved in private communications with the LayerZero team, and used by hundreds of other applications across the ecosystem.
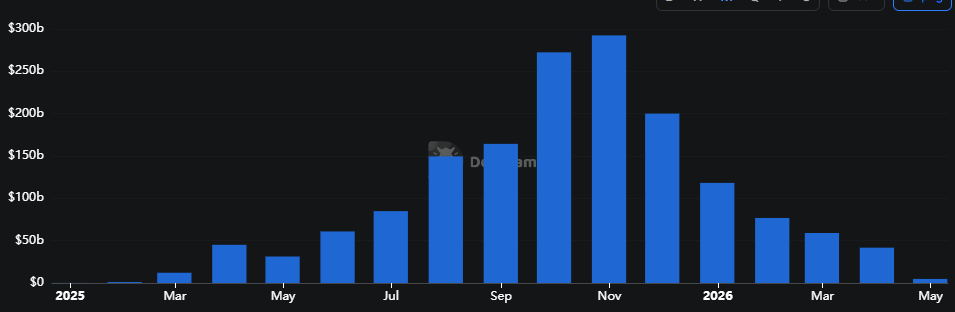
Kelp’s central argument is that the configuration LayerZero is now treating as a fringe choice was, in practice, the platform’s standard. The protocol points to public Dune data showing roughly 47% of LayerZero’s 2,665 active OApp contracts ran a 1-1 DVN security floor at the time of the exploit, with another 45% on 2-2 and only about 5% using 3-3 or higher.
In its post, Kelp published Telegram screenshots showing an alleged LayerZero Labs team member explicitly approving Kelp’s 1-1 configuration during the L2 expansion, alongside separate exchanges in which LayerZero assured the team its DVN was run with full monitoring and alerting.
Infrastructure Breach
Kelp’s second major argument is that the exploit originated inside LayerZero’s trust boundary. Citing reports from Seal911 and Yearn Finance core developer banteg, the protocol notes that the attackers, linked with high confidence to North Korea’s Lazarus Group, fraudulently triggered an attestation from the LayerZero Labs DVN by compromising RPC nodes that LayerZero itself operated.
Kelp argues LayerZero’s own postmortem confirms this when it refers to “our DVN” and “our least-privilege principles,” and pushes back on the framing of the event as a contained “RPC-spoofing attack.”
The team also notes that two additional forged transactions totaling more than $100 million were signed and processed by the LayerZero Labs DVN before being blocked when Kelp paused its contracts, and that LayerZero’s monitoring did not catch the compromise.
Open Questions
Kelp’s post lists four questions it wants LayerZero to answer publicly: how the RPC endpoint lists were accessed, how LayerZero’s documented defaults reconcile with the volume of 1-1 configurations across the ecosystem, why monitoring failed to detect the infrastructure compromise, and the dwell time of the compromised nodes before the forged message was signed.
Migration to Chainlink
Alongside the rebuttal, Kelp confirmed that rsETH will move to Chainlink’s CCIP and the CCT standard across all supported chains, with operational details being finalized by the engineering team. The Defi United coalition is separately working to restore the backing of rsETH and recover stolen tokens still held in attacker-controlled positions on Aave and Compound.
LayerZero has not yet responded publicly to Kelp’s rebuttal.
This article was written with the assistance of AI workflows. All our stories are curated, edited and fact-checked by a human.